2023 International Transplantation Science Meeting
The ITS 2023 committee is extending the abstract submission deadline to January 16, 2023 at 23:59 EST due to the general demand from the basic science community.
Transplantation Updates

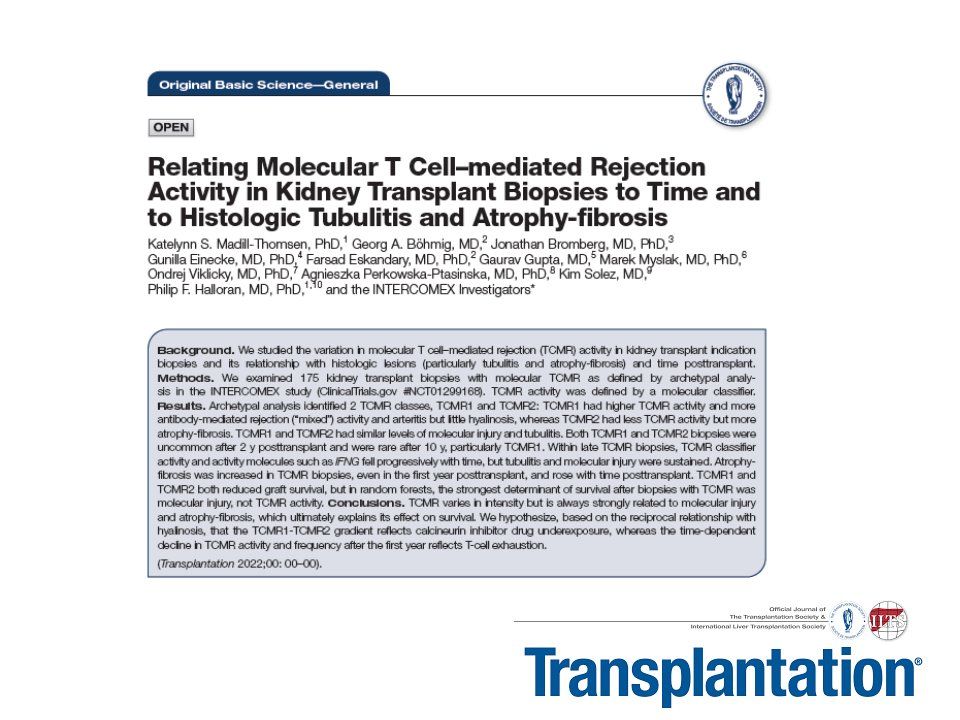
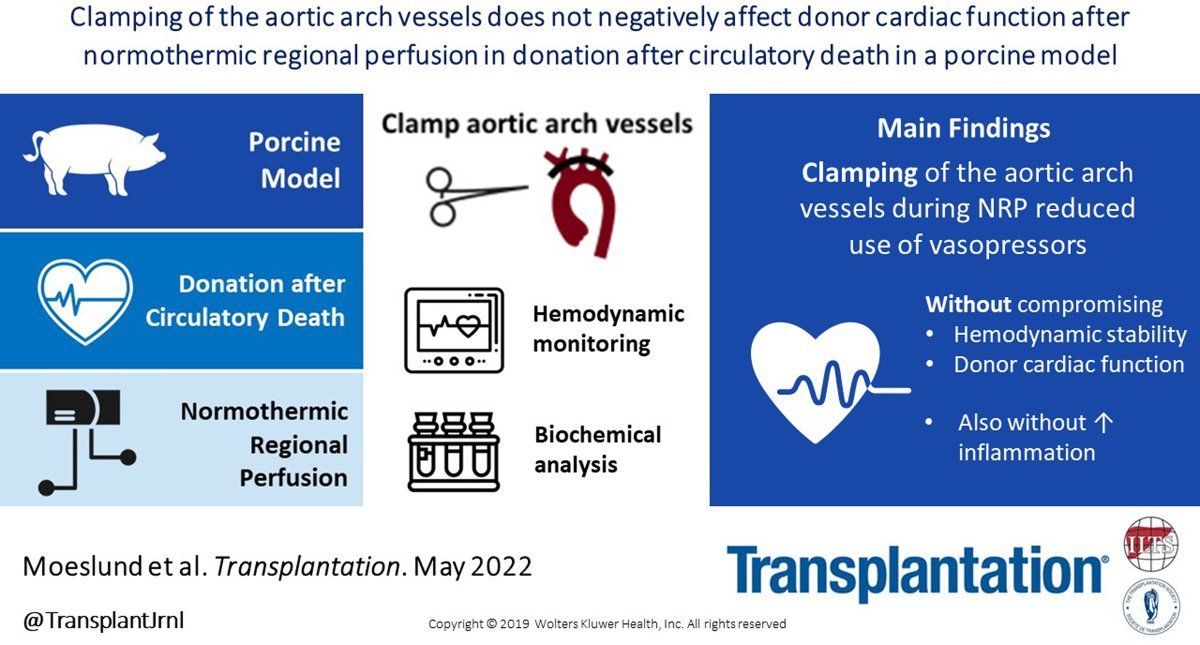
Transplantation - Highlighted Tweets
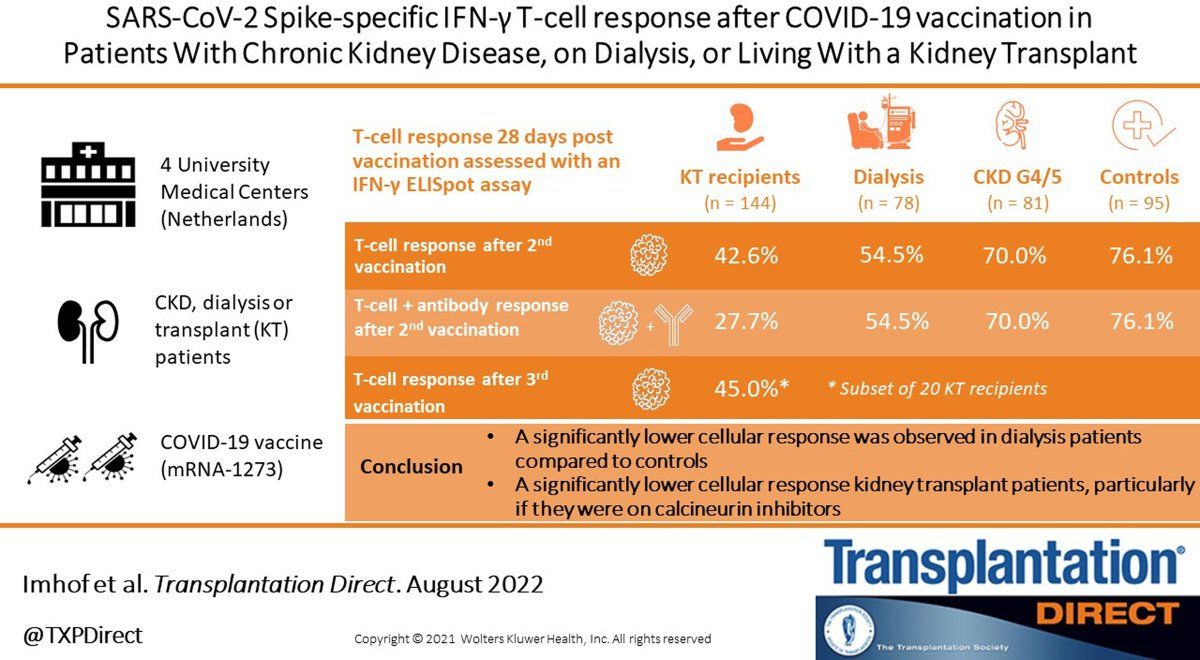
Transplantation Direct - Highlighted Tweets
This week some section members were targeted by fraudsters impersonating (spoofing) other members, urgently requesting money on behalf on another colleague utilizing non-TTS e-mail addresses (in this case aol.com emails).
FBI - Difference between Spoofing and Phishing schemes
https://www.fbi.gov/how-we-can-help-you/safety-resources/scams-and-safety/common-scams-and-crimes/spoofing-and-phishing
How to Recognize and Avoid Phishing Scams (by the USA Office of Inspector General)
https://consumer.ftc.gov/articles/how-recognize-and-avoid-phishing-scams
Google - Avoid and report phishing emails
https://support.google.com/mail/answer/8253?hl=en
The scheme is very simple and basic in the approach
Step 1: The fraudster creates an email account with a large email provider (aol.com, gmail, outlook, yahoo, hotmail, etc). They then use the name of the person they are impersonating, or an acronym of a recognizable institution (for example president.ipita@aol.com) in the user portion of the email address.
Step 2: They visit a website and scrape the names in the council list or committee members list then search for their email addresses on PubMed of Google.
Step 3: They will, in most cases, send emails requesting emergency financial assistance (stuck an an airport, lost their wallet, etc) and they will ask for you to call them or send money by western union, moneygram, worldremit. wise, etc). The common denominator is the amounts are usually <$1000 however they can be larger but usually with bigger amounts they will ask for a wire transfer. Usually they will try to get you on the phone or simply send you an email with how to send the money.
Step 4: If they get someone on the phone there is an added danger if they get you to log into a website or click a link while on the phone. This spoofing attempt may turn into a Phishing attempt to gain control of your computer.
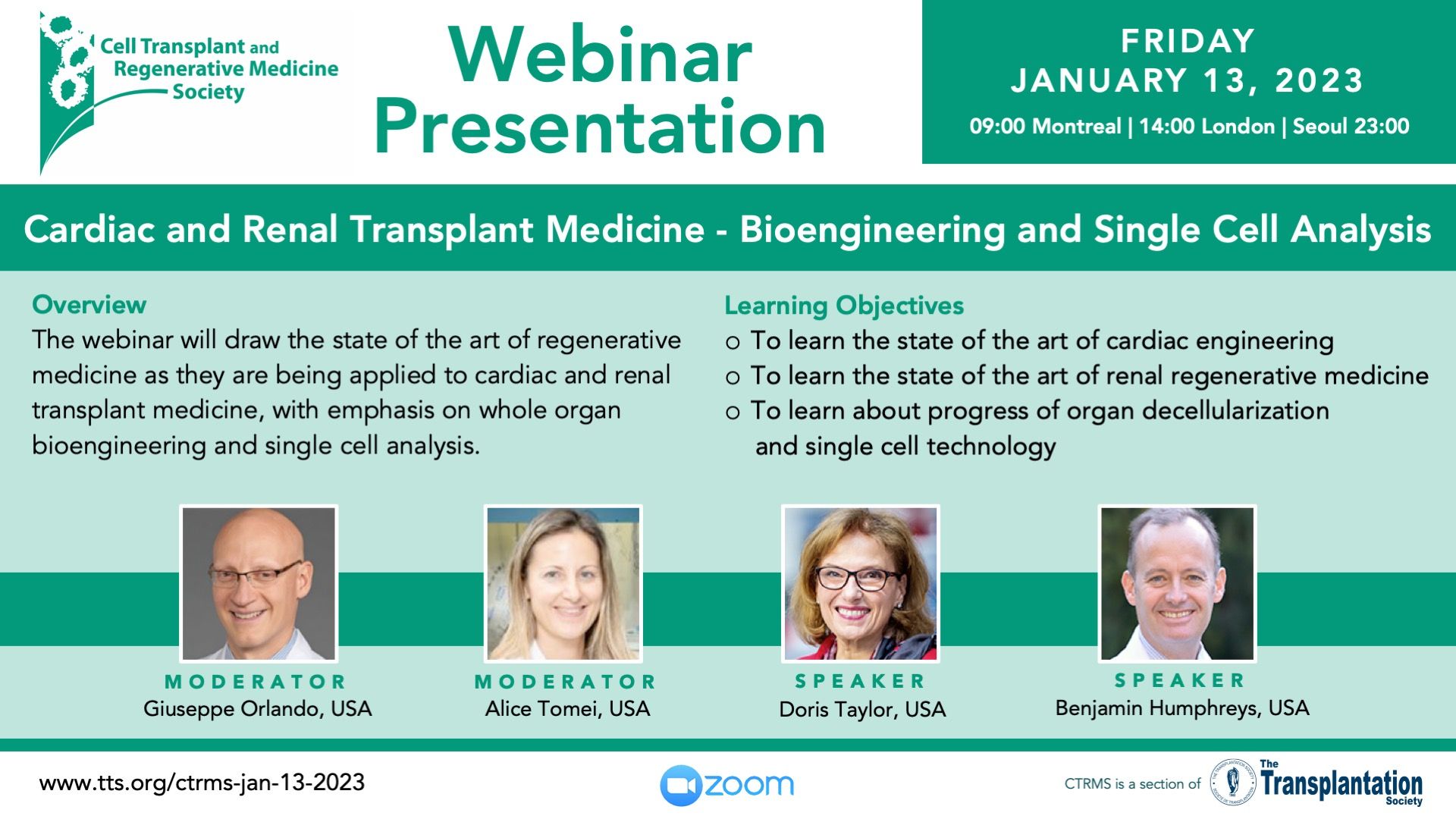
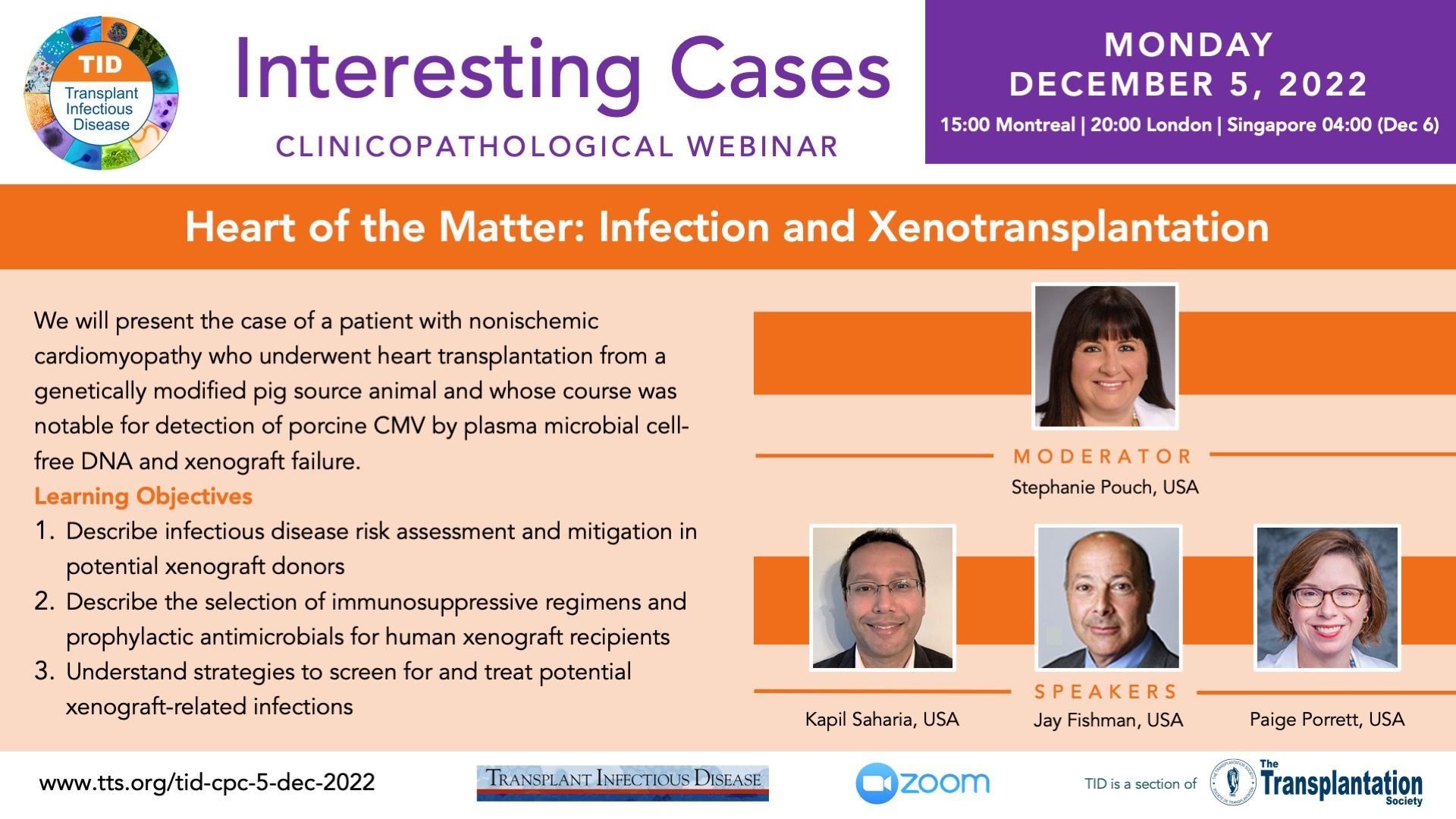
Latest Recordings
SPLIT is running a "4th Year Fellow Series" which includes talks on advanced hepatology and pediatric transplantation topics aimed to increase the knowledge of 4th year liver transplant fellows globally.
Contact
Address
The Transplantation Society
International Headquarters
740 Notre-Dame Ouest
Suite 1245
Montréal, QC, H3C 3X6
Canada
Используйте Вавада казино для игры с бонусом — активируйте промокод и начните выигрывать уже сегодня!